Getting started
Welcome to the Stormshield Data Security Enterprise administration guide version 11.4.2.
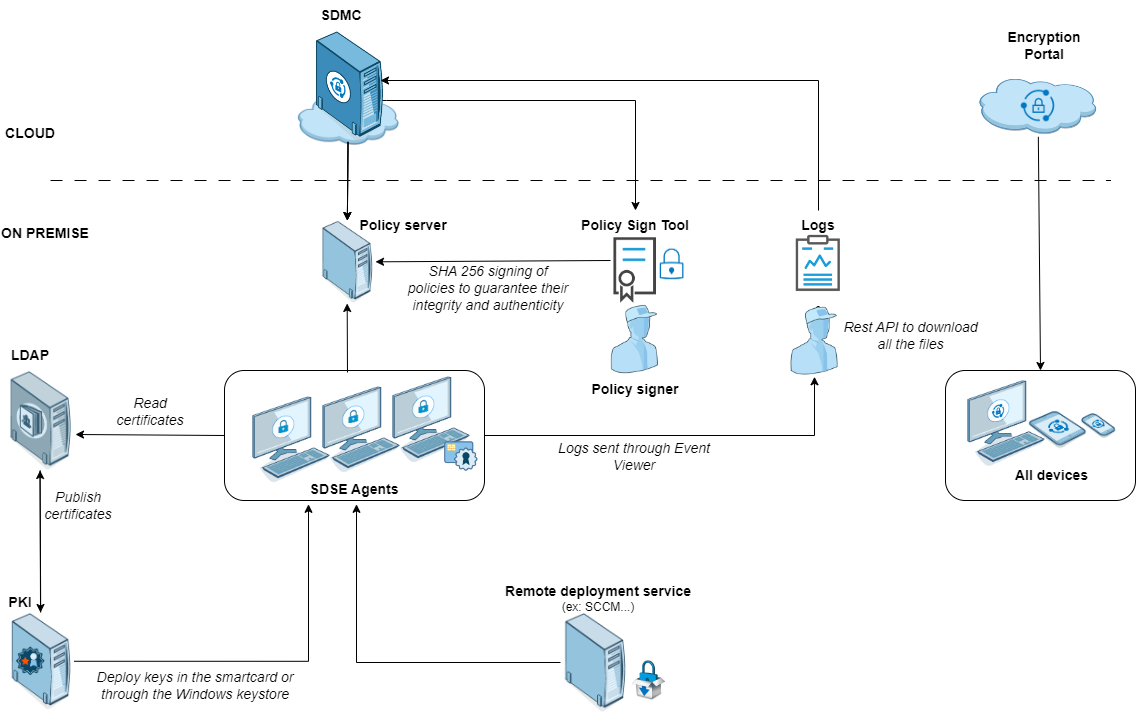
In the documentation, Stormshield Data Security Enterprise is referred to in its short form: SDS Enterprise and Stormshield Data Management Center as: SDMC.
This guide contains the information needed for managing SDS Enterprise and installing SDS Enterprise agents in your environment.
SDS Enterprise guarantees the protection and confidentiality of data stored on local, shared or cloud-based folders, by relying on the transparent end-to-end encryption built into communication and collaboration tools. With it, access to protected data can also be restricted to defined groups and user profiles.
SDS Enterprise includes the SDMC administration console, from which you can define security policies and an agent installed on users' workstations. This agent makes it possible to apply policies and provides the following features:
- Real-time transparent file encryption, for transfer by e-mail or secure backup,
- Encryption of files stored on spaces synchronized with online hosting services OneDrive, DropBox, SharePoint and Oodrive,
- Encryption and signature of e-mails, making it possible to protect the data that they contain, and guarantee the authenticity of their sender’s identity and the integrity of their contents,
- Sharing encrypted folders with coworkers over the corporate network,
- Secure and irreversible erasure of data,
- Electronic signature of files and folders, making it possible to guarantee the authenticity of their sender’s identity and the integrity of their contents,
- Encryption of virtual disks, making it possible to store protected files. These virtual disks can be shared among coworkers;
The solution also includes the
The SDMC administration console is hosted by Stormshield‘s Cloud services. In SDMC, you can:
-
Create and configure the security policies applied by the SDS Enterprise agents installed on users' workstations,
-
Declare the certification authorities on which user certificates depend,
-
Declare corporate LDAP directories to manage certificate exchanges,
-
Download SDS Enterprise agents' installation packages.
To use the SDMC console, start by creating a corporate account, then one or several administrator accounts as described in the section Logging in to SDMC.
You can also configure a security policy directly in a .json file and include it in the SDS Enterprise installation package. For more information on how to configuration this file, refer to the Advanced configuration guide.
Requirement
You must have an infrastructure to generate encryption and signature keys for the users in the company. You can then distribute them to users in whatever method you choose, for example via smart cards.
If you want to use the Microsoft Public Key Infrastructure solution, see Implementing the Microsoft Public Key Infrastructure (PKI) solution.
SDS Enterprise uses public key cryptography technology.
Each user has at least a pair of keys: a private key and a public key. The private key is carefully kept by its owner. The public key, by contrast, is freely distributed.
A different key pair is required for each purpose:
-
A pair of encryption keys is required for encrypting and sharing confidential files or e-mails,
-
A pair of signature keys is required to sign documents or e-mails,
To secure your users’ private keys, you can store them on cryptographic media that support the PKCS#11 standard. For single sign-on (SSO) user authentication, the keys must be stored in the Windows Certificate Store.
To encrypt files or send encrypted messages to peers, users must know their peers' public encryption key.
Public keys are distributed to users as certificates. A certificate is an electronic document that associates a public key with its owner. SDS Enterprise supports the X.509 V3 certificate format. These certificates are stored in users' trusted address book, as explained in the Understanding the notion of users' trusted address book section.
RSA keys of users and certification authorities must be a minimum size of 4096 bits, with a public exponent strictly greater than 65536. The certificates and CRLs must be signed with the SHA-512 algorithm.
IMPORTANT
When renewing encryption keys, make sure to keep the users’ old keys securely in their SDS Enterprise account. This will still allow the user to decrypt data encrypted with an old key.
For more information, see Decrypting user data with an old key or a delegation key and Decrypting user data with a recovery key.
For more information on managing certificates, refer to the sections Managing authority certificates and recovery certificates in SDMC and Setting account creation parameters.
You can deploy SDS Enterprise to user workstations with remote distribution solutions such as Microsoft Endpoint Configuration Manager. You must deploy on the workstations:
-
the SDS Enterprise agent installation package in the .msi format. You can download it from the SDMC console in French and English.
-
deploying the signed security policy file and the peer certificate. The policy is created and configured in the SDMC console. You must download it from the console and have it signed by the administrator who has the role of security policy signatory. The signature utility is also available in SDMC.
Each time the SDS Enterprise agent restarts, it checks if a new policy update is available on the server that acts as the policy distribution point. If this is the case, it will apply it automatically.
For further information on agent deployment, refer to the Installing SDS Enterprise agents on the user stations and deploying the security policies section.
SDS Enterprise makes it possible to manage a trusted address book on users' workstations: you can add the certificates (public keys) of the users and authorities that you trust in the address book.
Users can be automatically added to the trusted address book via an LDAP directory.
For more information, refer to the sections Managing LDAP directories in SDMC and Configuring corporate directories.