Updating BIOS and the Intel Management Engine firmware
This section sets out the steps to follow in order to update BIOS on SN-L-Series (SN-L-Series-2200 and SN-L-Series-3200) model firewalls to version R1.06 in console mode from a USB drive.
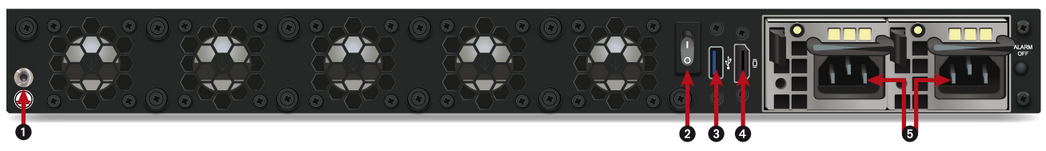
Connecting devices to SNS firewalls
-
Connect the computer to the SNS firewall using a USB-A to USB-C cable (SNS firewall side) or an RJ45 to DB9 serial cable (RS232).
- or -
- Connect a USB keyboard and a monitor to the SNS firewall using an HDMI cable.
| Front panel | Rear panel | |
|
|
|
|
|
1: USB-C serial port in console mode 2: RJ45 serial port in console mode 3: USB 3.0 port |
1: On/off button 2: USB 3.0 port 3: HDMI port: for plugging in the monitor 4: Mains sockets for redundant power supplies |
Checking the current BIOS version
- Log in to the SNS firewall system in console or SSH mode.
- Authenticate by using the admin account on the SNS firewall system.
-
Enter the command:
dmidecode -s bios-version
The SNS firewall should show version R1.02 or R1.05.
Disabling Secure Boot
The update procedure requires Secure Boot to be disabled so that the SNS firewall can start up on the USB drive that was prepared earlier.
To disable Secure Boot, refer to the section SN-L-Series-2200 and SNS-L-Series-3200 in the technical note Managing Secure Boot in SNS firewalls' UEFI.
Updating BIOS
IMPORTANT
The update process is automatic and lasts around five minutes. Once the process is run, it must never be interrupted, and the SNS firewall must not be disconnected from the power supply. If this occurs, the SNS firewall will be completely unable to run.
- As SN-L-Series firewalls have two internal power supply units to provide a redundant power supply, ensure that you have plugged in both power cords to the electrical mains.
- Insert the USB drive that was prepared earlier into a USB port.
-
Restart the SNS firewall by using the command:
reboot
-
In the command prompt, run the executable file:
Flash_SNL_R106.nsh
The update process will then start:
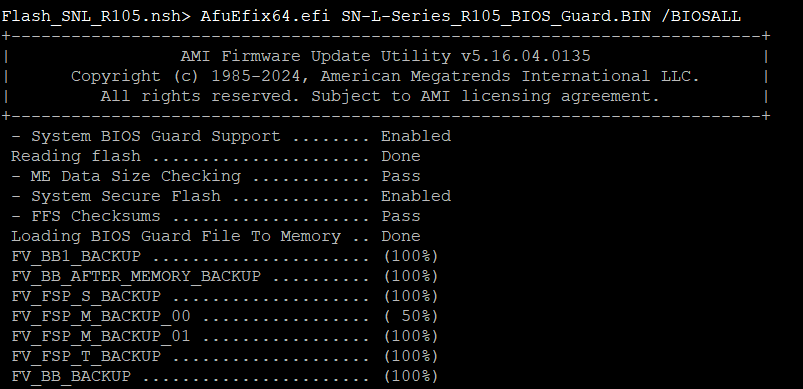
-
When the update is complete, restart the SNS firewall by using the command:
reset
Disabling Secure Boot again
After a BIOS update, Secure Boot will be enabled once again. You will need to disable it again by referring to the section SN-L-Series-2200 and SN-L-Series-3200 in the technical note Managing Secure Boot in the SNS firewalls' UEFI.
Updating the Intel Management Engine firmware
-
Restart the SNS firewall by using the command:
reboot
-
In the command prompt, run the executable file:
Flash_ME_SNL.nsh
The update process will then start:
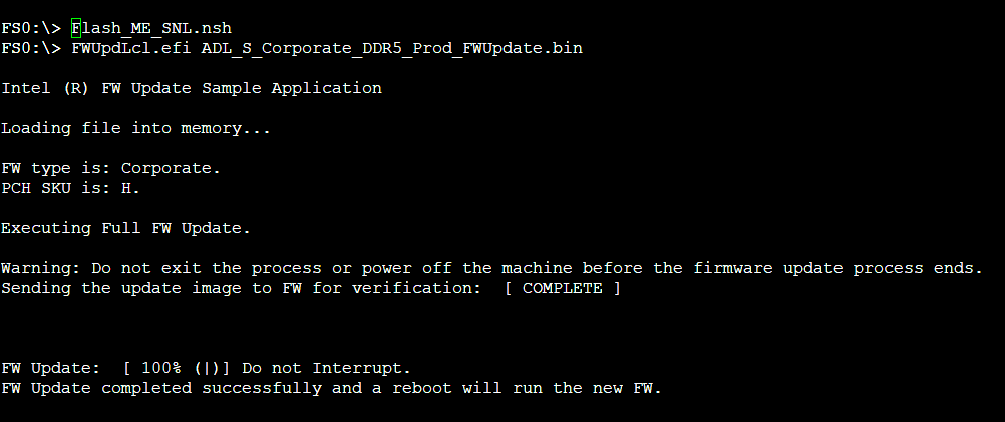
-
When the update is complete, shut down the SNS firewall by using the command:
reset -s
- Unplug both power cables from the SNS firewall.
- Unplug the USB drive from the SNS firewall.
- Wait five minutes.
- Plug in both power cables.
- Start the SNS firewall by holding down the Power button located on the rear panel.
Checking the BIOS and Intel Management Engine firmware versions after the update
- Once the SNS firewall starts up, press [Del] several times to stop its startup sequence, and access BIOS.
- Go to the Main tab and check the following versions:
- BIOS Version field: the version that appears should be R1.06.
- ME Firmware Version field: the version that appears should be 16.1.38.2676.
- Quit BIOS.
Required operations following an update
Once you have updated BIOS, launch the following operations, in this order.
Configuring the password to access the UEFI control panel
If you had set a password to access the UEFI control panel, the password will be deleted if BIOS is being updated from version R1.02. To set a new password, refer to the technical note Protecting access to the configuration panel of the UEFI on SNS firewalls.
If BIOS is being updated from version R1.05, you do not need to perform any operation as the password will be retained.
Enabling Secure Boot
You will need to enable Secure Boot again by referring to the section SN-L-Series-2200 and SN-L-Series-3200 in the technical note Managing Secure Boot in the SNS firewalls' UEFI.
Resealing the TPM
If you had initialized the TPM, the features that use certificates with TPM-protected private keys (VPN, SMC-managed firewall, etc.) will no longer function. To restore the features in question, follow one of the procedures below to reseal the TPM.
From the web administration interface
This use case is exclusive to SNS 4.8.7 and higher versions.
-
Log in to the SNS firewall web administration interface. A window prompts you to seal the TPM module of the SNS firewall.
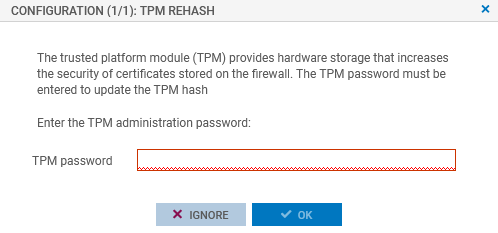
- Enter the TPM module administration password in the relevant field.
- Click on OK.
- If the SNS firewall is part of a high availability cluster, a second window prompts you to seal the TPM module of the passive firewall. Enter the TPM module administration password and click on OK.
From the CLI console
Seal the TPM on the SNS firewall with the command:
SYSTEM TPM PCRSEAL tpmpassword=<password>
Replace <password> with the TPM module administration password.
If the SNS firewall is part of a high availability cluster, seal the TPM on the passive firewall with the command:
SYSTEM TPM PCRSEAL tpmpassword=<password> serial=passive