Configuring the authentication method and policy
Configuring the authentication method
- Go to Configuration > Users > Authentication, Available methods tab.
- Click on Add a method or Enable a method (according to the version installed on the SNS firewall).
- Select SSO Agent from the drop-down list.
- In the section on the right, in the Domain name field, select the Active Directory domain associated with SN SSO Agent from the drop-down list.
- Continue with the configuration section by section according to the parameters below.
Enter the information about the main SN SSO Agent:
- IP address: from the drop-down menu, select the network object that corresponds to the host on which SN SSO Agent is installed.
- Port: the port "agent_ad" is selected by default, corresponding to port 1301. The protocol used is TCP.
- Pre-shared key (password): enter the key defined during the installation of SN SSO Agent.
This key is used to encrypt exchanges between SN SSO Agent and the firewall in SSL.
The strength of the pre-shared key indicates this password’s level of security. You are strongly advised to use uppercase and special characters.
You can also specify this information for a backup SN SSO Agent (optional).
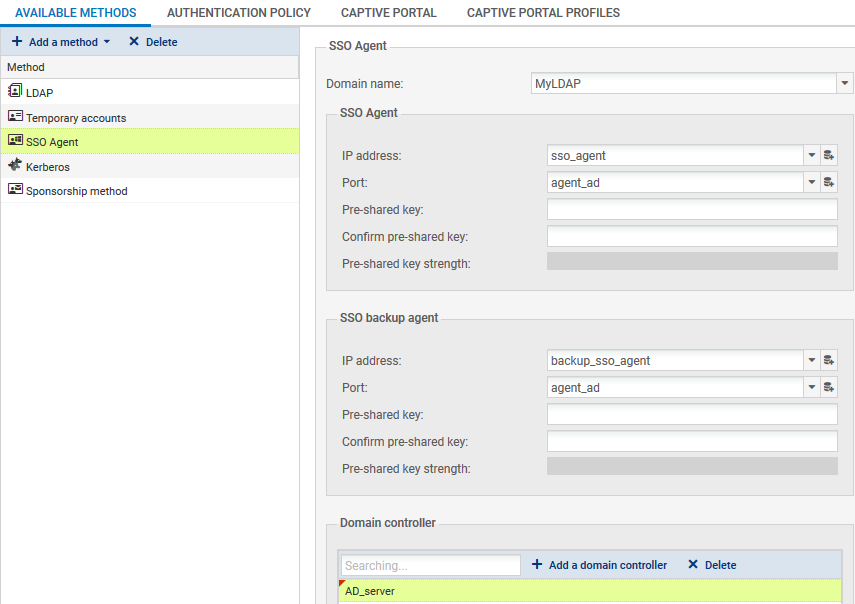
You will need to add all the domain controllers that control the Active Directory domain. They must be saved beforehand in the firewall’s Network objects database.
If several domain controllers manage the domain, the account that SN SSO Agent uses must be a dedicated account belonging to the domain, with the privileges described in the chapter Configuring access to Active Directory. These privileges must apply to all domain controllers so that all events occurring on the domain can be relayed.
Maximum authentication duration: define the maximum duration of an authenticated user’s session. After this duration is exceeded, the firewall will delete the user associated with this IP address from its table of authenticated users, logging the user out of the firewall.
This limit is to be defined in minutes or hours, and is set by default to 10 hours.
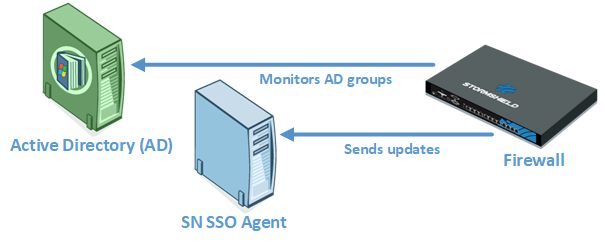
Refresh user groups updates: for each Active Directory configured on the firewall (Directory configuration), the firewall will check for any changes to the LDAP directory groups. It then updates its directory configuration, and sends back this information to SN SSO Agent.
This limit is to be defined in minutes or hours, and is set by default to 1 hour.
Disconnection detection: by enabling the disconnection method, authenticated users can be deleted when a host is logged out or when a session is shut down. If this method is not enabled, the user will be unauthenticated after the set authentication period, even when the session has been shut down.
To test which hosts are logged in to the firewall, you can either ping them or look up the registry database.
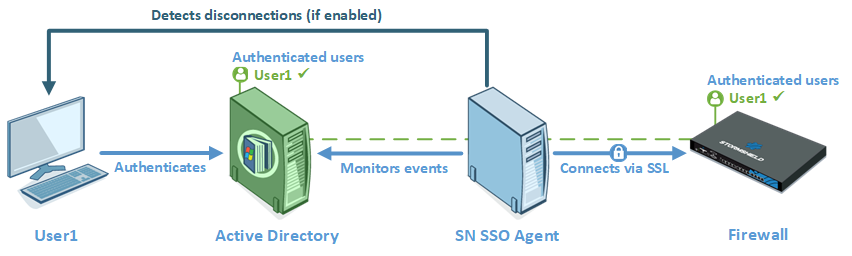
- PING: SN SSO Agent tests the accessibility of all hosts authenticated on the firewall every 60 seconds by default.
If it gets a host unreachable response or no response is received from an IP address after the period defined below, SN SSO Agent will send a logoff request to the firewall. The firewall will then will delete the user associated with this IP address from its table of authenticated users, logging the user out of the firewall.
Hosts on the domain must allow responses to ping tests (parameters of the Windows firewall on workstations). On the other hand, if SN SSO Agent passes through a firewall to access hosts on the domain, rules have to be created to allow SN SSO Agent to test the workstations in the firewall’s filter policy. - Registry database: this method makes it possible to detect, for example, a closed session on a host that is still running. If a positive response to the ping is received, SN SSO Agent will log in remotely to the host and check in the Registry database the list of users with a session open on the host. This allows the registry database to update its table of authenticated users.
To set up the Registry database method, you must meet the following conditions:- The account associated with SN SSO Agent must have administration privileges on all hosts authenticated on the firewall; this account must belong to the group Administrator of the Active Directory server or be defined as a local administrator on monitored machines (see the chapter Configuring access to Active Directory).
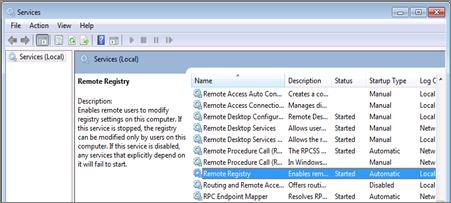
- The Remote registry service has to be enabled on these hosts. To do so, go to Services in Windows, select the service Remote registry then click on Start. The status of this service must also be changed from Manual to Automatic.
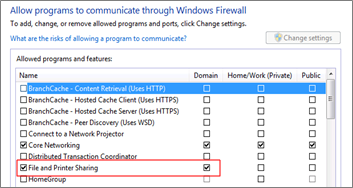
- Ports 139 and 445 (Windows ports) & ICMP have to be open. Follow the path Control panel > System and security > System > Windows firewall and click on Allow programs to communicate through Windows firewall, then select File and printer sharing.
- This method requires the configuration of the opposite zone of the domain on the DNS server in order to detect changes in IP addresses (if a DHCP address is renewed, for example). Refer to the section Changing an IP address in Specific cases for more information.
Consider as disconnected after: if a host does not respond to the ping after this period, it will be considered disconnected. The firewall will then delete the user associated with this host from its table of authenticated users. This duration defined in seconds or minutes is set by default to 5 minutes.
Ignored administration accounts: in the firewall’s factory configuration, there is a list of users whose authentication is ignored. These accounts list the usual logins dedicated to the administrator (Administrator and Administrateur by default).
This mechanism was set up because the domain controller treats the execution of a service or an application (Run as administrator feature, for example) as an authentication. As SN SSO Agent restricts authentication by IP address, this type of authentication may potentially replace the authentication of the user with an open Windows session.
The pre-set list of “Ignored Administrator accounts” allows SN SSO Agent to ignore their authentication. Edit it if necessary.
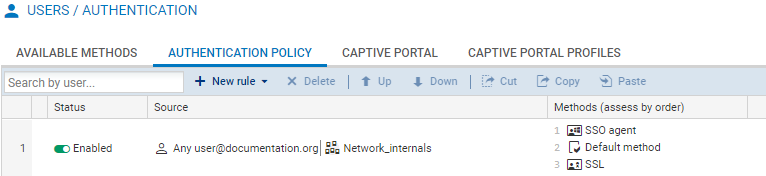
Configuring the authentication policy
To allow traffic dedicated to the SSO Agent authentication method that was configured, you must define rules in the Authentication policy.
- Go to Configuration > Users > Authentication, Authentication policy tab.
- Click on New rule.
- Select Standard rule to run the wizard.
- Under the User tab, in the User or group field: select the user or group concerned or leave the default value Any_user@selected_domain.
- In the Source tab: click Add an object to target the source of the traffic to which the rule applies. This may be the object corresponding to these internal networks (e.g.: network_internals).
The SSO agent authentication method is based on authentication events collected by domain controllers. Since these events do not indicate the source of the traffic, interfaces cannot be specified in the authentication policy. - In the Authentication methods tab: click on Enable a method and select from the drop-down list the authentication methods to apply to the traffic affected by the rule.
They are evaluated in the order in which they appear on the list and from top to bottom. As the SSO agent method is transparent, it is by definition always applied as a priority.
The Default method can be modified below the table containing the rules of the authentication policy - Click on OK, then on Apply.
The SSO Agent method does not support multi-user objects, i.e., several authenticated users on the same IP address. However, such objects can be contained in a network, address range or a group defined as the source of a rule that uses the SSO Agent method.
To avoid having multiple logs regarding SN SSO Agent being denied for users on an address declared as a multi-user address, you are advised to add two rules dedicated to these objects in front of the rules that use the SSO Agent method:
- the first rule specifies the method used by the multi-user object
- followed by a second rule that will “block” the authentication of this object in order to block any other authentication attempts.