Configuring the FW-PARIS firewall
Creating objects corresponding to LANs at the PARIS and LILLE sites
- Go to Configuration > Objects > Network.
- Click on Add.
- In the column on the left side of the object creation window, select Network.
- Specify the Object name (LIL-LAN in this example).
- Enter the Network IP address in the form of a network/mask. The network mask can be entered in CIDR or decimal format.
- Click on Create and duplicate.
- Repeat steps 4 and 5 to create the object PAR-LAN.
- Click on Create.
Creating objects corresponding to the PARIS WAN gateways/links
- Go to Configuration > Objects > Network.
- Click on Add.
- In the column on the left side of the object creation window, select Host.
- Specify the Object name (PAR-WAN-1 in this example).
- Enter its IPv4 address.
- Click on Create and duplicate.
- Repeat steps 4 and 5 to create the object PAR-WAN-2.
- Click on Create.
Creating objects corresponding to the LILLE WAN gateways/links
- Go to Configuration > Objects > Network.
- Click on Add.
- In the column on the left side of the object creation window, select Host.
- Specify the Object name (LIL-WAN-1 in this example).
- Enter the public IPv4 address of the LILLE site's WAN-1 link.
- Click on Create and duplicate.
- Repeat steps 4 to 5 to create the object LIL-WAN-2 with the public IPv4 address of the LILLE site's WAN-2 link.
- Click on Create.
Creating objects corresponding to the virtual IPsec interfaces of the LILLE firewall
- Go to Configuration > Objects > Network.
- Click on Add.
- In the column on the left side of the object creation window, select Host.
- Specify the Object name (LIL-VTI-1 in this example).
- Enter the IPv4 address of the virtual IPsec interface (10.255.1.1/ 255.255.255.252).
- Click on Create and duplicate.
- Repeat steps 4 to 5 to create the object LIL-VTI-2 with the IP address 10.255.2.1/255.255.255.252 in this example.
- Click on Create.
Creating virtual IPsec interfaces for the PARIS site
- Go to Configuration > Network > Virtual interfaces.
- Click on Add.
- Switch the Status of the interface to Enabled.
- Indicate the Name of the virtual IPsec interface (PAR-VTI-1 in this example).
- Indicate the IPv4 address and network mask of this interface (10.255.1.2/255,255,255,252 in this example).
- Click on Apply.
- Repeat steps 2 to 6 to create the second virtual IPsec interface (PAR-VTI-2 and 10.255.2.2/255.255.255.252 in this example).
- Click on Apply at the bottom of the module to save this configuration.
Creating return routes for the FW-PARIS virtual IPsec interfaces
- Go to Configuration > Network > Routing, IPv4 return routes tab.
- Click on Add.
- Switch the Status of the return route to On.
- Indicate the remote Gateway of this return route (LIL-VTI-1 in this example).
- Indicate the local virtual IPsec interface to be used for this return route (PAR-VTI-1 in this example).
- Repeat steps 2 to 5 with the following elements:
- Gateway: LIL-VTI-2,
- Interface: PAR-VTI-2.
- Click on Apply at the bottom of the module to save this configuration.
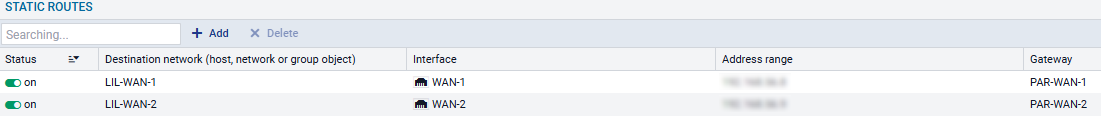
Creating the static routes required for setting up IPsec tunnels
This step involves defining a static route to each physical remote interface in such a way that:
- The first tunnel sets up between the links LIL-WAN-1 and PAR-WAN-1,
- The second tunnel sets up between the links LIL-WAN-2 and PAR-WAN-2.
To do so:
- Go to Configuration > Network > Routing > Static routing tab.
- Click on Add.
- Switch the Status of the route to On.
- For the Destination network, select the object corresponding to the LILLE site's WAN 1 access link (LIL-WAN-1 in the example).
- For the local Interface that needs to be used for this route, select the interface corresponding to the PARIS WAN 1 access link (WAN-1 in this example).
- For the gateway that needs to be used for this route, select the object PAR-WAN-1.
- Repeat steps 2 to 6 with the following elements:
- Destination network: LIL-WAN-2,
- Interface: WAN-2,
- Gateway: PAR-WAN-2.
- Click on Apply at the bottom of the module to save this configuration.
These routes will then resemble the following:
Creating the router object to use in the route to the LILLE site's LAN
- Go to Configuration > Objects > Network.
- Click on Add.
- In the column on the left side of the object creation window, select Rrouter.
General properties
- Name the object (e.g., ROUTER-PARIS-VTI-FAILOVER or ROUTER-PARIS-VTI-LB depending on the chosen routing option).
Monitoring
- For the Detection method, select ICMP.
- Adjust the Timeout (s) as needed.
- Adjust the Interval (s) as needed.
- Adjust the number of Failures before degradation (3 by default).
SD-WAN SLA (thresholds)
- Select SD-WAN SLA (thresholds).
- Adjust the Latency (ms) as needed.
- Adjust the Jitter (ms) as needed.
- Adjust the Packet loss rate (%) as needed.
- Do not enter an Unavailability rate (%).
Gateways
- In the Gateways used tab, click on Add.
- In the Gateway column, select the object LIL-VTI-1.
- In the Device(s) for testing availability column, select Test the gateway directly.
- If you select the load balancing option: repeat steps 14 to 16 to add the object LIL-VTI-2.
- If you select the failover option:
- In the Backup gateways tab, click on Add.
- In the Gateway column, select the object LIL-VTI-2.
- In the Device(s) for testing availability column, select Test the gateway directly.
Advanced properties
- In Advanced properties, for the Load balancing field value:
- Depending on your requirements, select By connection or By source IP address if you have chosen the load balancing option.
- Select No load balancing if you have chosen the failover option.
- For Enable backup gateways, select When all gateways cannot be reached.
- Click on Apply then Save.
For the If no gateways are available field, select Do not route regardless of your routing choice.
This will prevent unencrypted traffic from being sent to unprotected networks, such as the Internet if no gateways are available.
Using this object in routing to reach the LILLE site's LAN
Static routing with backup
- Go to Configuration > Network > Routing > Static routing tab.
- Click on Add.
- Switch the Status of the return route to Enabled.
- For the Destination network, select the object corresponding to the LILLE site's LAN (LIL-LAN in the example).
- Do not select any interface.
- For the gateway that needs to be used for this route, select the router object that was configured with failover (ROUTER-PARIS-VTI-FAILOVER in this example).
- Click on Apply at the bottom of the module to save this configuration.
This route will then look like this:

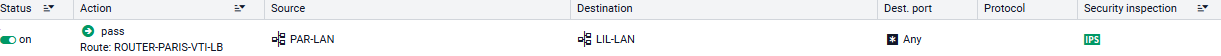
Policy-based routing with load balancing
- Go to Configuration > Security policy > Filter - NAT, Filtering tab.
- Click on New rule > Single rule.
- Double-click in any column in this rule.
- General menu on the left: switch the Status of the rule to On.
- Action menu on the left, General tab:
- General section: set the Action to pass.
- Routing section: select the router object that was configured earlier (ROUTER-PARIS-VTI-LB in this example).
- Source menu on the left: double-click on the Any object and replace it with the object corresponding to the local network of the PARIS site (PAR-LAN in this example).
- Destination menu on the left: double-click on the Any object and replace it with the object corresponding to the local network of the LILLE site (LIL-LAN in this example).
- Port/Protocol menu on the left: add to the grid the Destination ports of the various objects corresponding to the ports to be allowed in this filter rule.
- Inspection menu on the left: we recommend leaving the default Inspection level, IPS.
- Click on OK.
- Click on Apply.
This filter rule will then look like this:
Setting the IPsec peers of the LILLE site
This peer is a remote gateway.
In this example, pre-shared key authentication is used.
In order for one of the two FW-PARIS WAN links to be used when the tunnel is initialized, the value of the Local address field has to be Any. Similarly, the DPD (Dead Peer Detection) option has to be set to High to force the IPsec tunnel to be renegotiated as quickly as possible when the link is down.
- Go to Configuration > VPN > IPsec VPN > Peers tab.
- Click on Add, then on New remote gateway.
- In the Remote gateway field, select the object corresponding to the FW-LILLE firewall's first public IP address (LIL-WAN-1 in the example).
- Enter a name for this peer (LIL-WAN-1 in the example).
- Select the IKEv2 version.
- Choose the IKE profile to use.
- Click on Next.
- For the Authentication type, select Pre-shared key (PSK).
- Set the Pre-shared key and confirm it.
- Click on Next.
You will be shown a summary of the peer's details. - Click on Finish.
Details on the peer are shown. - Ensure that the value of the Local address is Any.
- In the Advanced properties section, set the DPD field to High.
- Click on Apply then on Save.
- Repeat steps 2 to 14 to create the peer based on the FW-LILLE firewall's second public IP address (LIL-WAN-2 in this example).
- Changes can be applied immediately by clicking on Yes, activate the policy.
Creating the IPsec policy to set up tunnels with the LILLE site
- Go to Configuration > VPN > IPsec VPN > Encryption Policy - Tunnels tab > Site-to-site (gateway-gateway) tab.
- Click on Add, then on Standard site-to-site tunnel.
- In the Local resources field, select the traffic endpoint of the PARIS site: this is FW-PARIS's first virtual IPsec interface (network object Firewall_PAR-VTI-1 in the example).
- In the Peer selection field, select the first peer that was created for the PARIS firewall (host object LIL-WAN-1 in the example).
- In the Remote networks field, select the traffic endpoint of the PARIS site: this is FW-PARIS's first virtual IPsec interface (network object LIL-VTI-1 in the example).
- Click on Finish.
- Click in the Keepalive column and select a duration from the drop-down menu (600 ms in the example).
This setting determines how long to keep the tunnel up even when it is not in use. - Double-click in the Status column to enable this rule in the IPsec policy.
- Repeat steps 2 to 8 to create the tunnel between LIL-VTI-2 and PAR-VTI-2.
- Click on Apply then on Save.
- Changes can be applied immediately by clicking on Yes, activate the policy.
On the FW-PARIS firewall, the IPsec policy between the LILLE and PARIS sites is therefore:

Creating the filter rule to enable monitoring of VTIs at the LILLE site
- Go to Configuration > Security policy > Filter - NAT, Filtering tab.
- Click on New rule > Single rule.
- Double-click in any column in this rule.
- General menu on the left: switch the Status of the rule to On.
- Action menu, General tab: set the Action to pass.
- Source menu on the left: leave the Any object suggested by default.
- Destination menu on the left: select the objects corresponding to the PARIS site's VTIs (LIL-VTI-1 and LIL-VTI-2 in this example).
- Port/Protocol menu on the left: for the IP protocol field in the Protocol section, select the icmp object.
- Inspection menu on the left: we recommend leaving the default Inspection level, IPS.
- Click on OK.
- Click on Apply.
Creating the filter rule to enable dialogue between the LILLE and PARIS sites
- Go to Configuration > Security policy > Filter - NAT, Filtering tab.
- Click on New rule > Single rule.
- Double-click in any column in this rule.
- General menu on the left: switch the Status of the rule to On.
- Action menu, General tab: set the Action to pass.
- Source menu on the left: double-click on the Any object and replace it with the object corresponding to the local LILLE network (LIL-LAN in this example).
- Destination menu on the left: double-click on the Any object and replace it with the object corresponding to the local PARIS network (PAR-LAN in this example).
- Port/Protocol menu on the left: add to the grid the Destination ports of the various objects corresponding to the ports to be allowed in this filter rule.
- Inspection menu on the left: we recommend leaving the default Inspection level, IPS.
- Click on OK.
- Repeat steps 2 to 10 with the PAR-LAN object as the source, and the LIL-LAN object as the destination.
- Click on Apply.
The second rule does not need to be created if you have used policy-based routing to reach the LILLE LAN.