Getting started
Products concerned: SNS 4.3.15 and later versions of 4.3 branch, SNS 4.5.3 and higher versions
Last update: February 2023
Quality of Service (QoS) and its components
Quality of service refers to any technology that can manage data transmission while reducing packet loss, latency and jitter for high-priority traffic on the network. The aim of this concept is to monitor and manage network resources by prioritizing certain types of data and network traffic.
There are two ways in which traffic is managed:
- Bandwidth reservation for high-priority traffic or traffic with high technical constraints (e.g., work flows or telephony over IP),
- Bandwidth limitation for lower-priority traffic (e.g., web browsing).
NOTE
Bandwidth reservation or limitation is applied to traffic when it leaves the network interface on which QoS has been enabled. So, these mechanisms do not have any real impact on incoming traffic, such as downloads.
Regulation mechanism: difference in the behavior of TCP and UDP traffic
When TCP traffic exceeds the bandwidth limit set in a QoS queue, the regulation mechanism will reject some of these TCP packets and slow down traffic leaving the interface. The sender of the TCP traffic will then realize that packets were lost along the way and slow down throughput until it meets the firewall's QoS configuration criteria.
As this regulation mechanism does not exist for UDP traffic, incoming throughput on the interface will never adapt to the QoS configuration; it will also not comply with all bandwidth reservations on the incoming interface, and even disrupt them.
QoS queues
For these reservation and limitation operations, the queues that will be assigned to QoS-enabled network interfaces must be defined.
There are three possible types of queues:
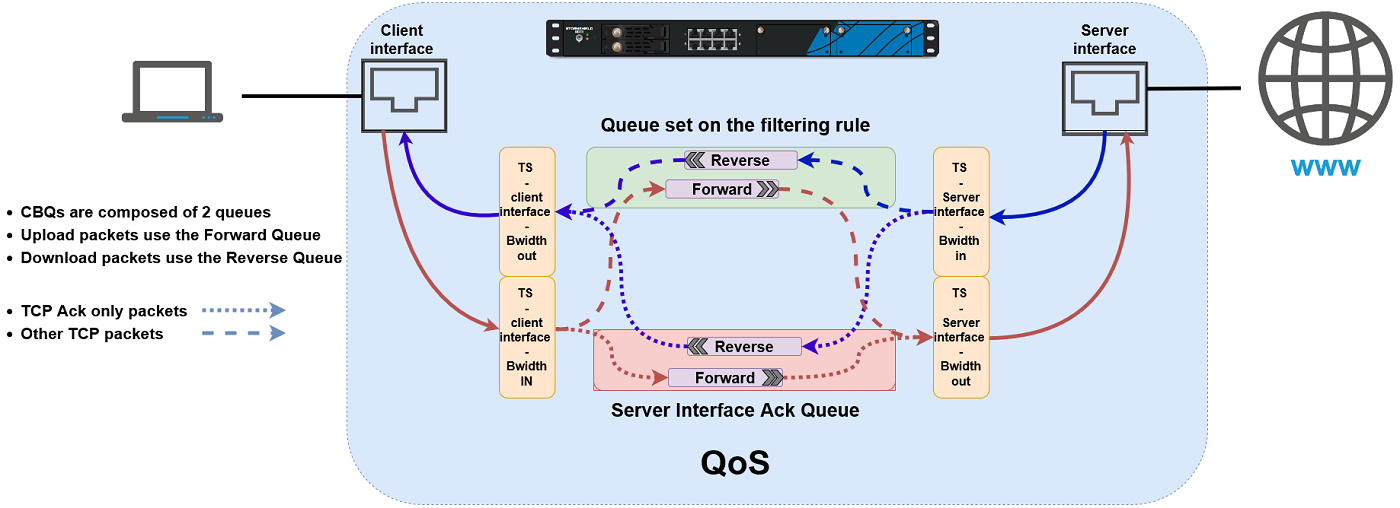
- Class-Based Queuing or CBQ: these queues are used for reserving or limiting bandwidth by indicating the maximum or guaranteed bandwidth to apply,
- Priority Queuing or PRIQ: in these queues, packets are prioritized and classified from priority 0 (traffic with the highest priority) to priority 7 (traffic with the lowest priority).
Packets associated with a filter rule that uses a PRIQ are processed before packets that are not assigned to a PRIQ, or which are attached to a PRIQ with lower priority. - To prevent the risk of traffic congestion, such queues must be reserved for throughput-controlled traffic that cannot consume all the bandwidth, and must be reserved for traffic with the highest priority.
- We strongly recommend having a single PRIQ that can deprive the other queues and assign to it a lower priority than for other queues. For example, do not create a PRIQ for HTTP and another for FTP.
- You are advised against using more than three or four levels of priority in a configuration.
- Do not combine PRIQs and CBQs in the same configuration.
Even though the web administration interface does not prohibit the combination of CBQs and PRIQs, Stormshield does not support such configurations. - Monitoring Queuing or MONQ: these specific queues do not have any impact on network traffic but make it possible to save and present in graphs (Monitoring > Monitoring > QoS module) information about the bandwidth used by the traffic to which these queues were assigned. This makes it possible to set or refine the configuration of CBQs.
The volume of data exchanged is regulated by a traffic shaper associated with QoS queues. This traffic shaper applies to the outgoing interface of processed packets.
DEFINITION
The aim of traffic shaping is to enforce the Committed Information Rate (CIR) through the regulation of data volume exchanged over the network, by delaying packets that meet the criteria defined in the queues (reservation or limitation). The mechanism runs on an algorithm named TBR (Token Bucket Regulator) which uses a buffer for excess traffic.
IMPORTANT
QoS cannot be implemented on traffic shapers with bandwidth higher than 1 Gbit/s.
NOTE
In configurations that use IPsec traffic, such traffic will automatically join the default queue for the WAN interface. This is why class-based queuing is applied to this queue.
Illustration: overview of QoS
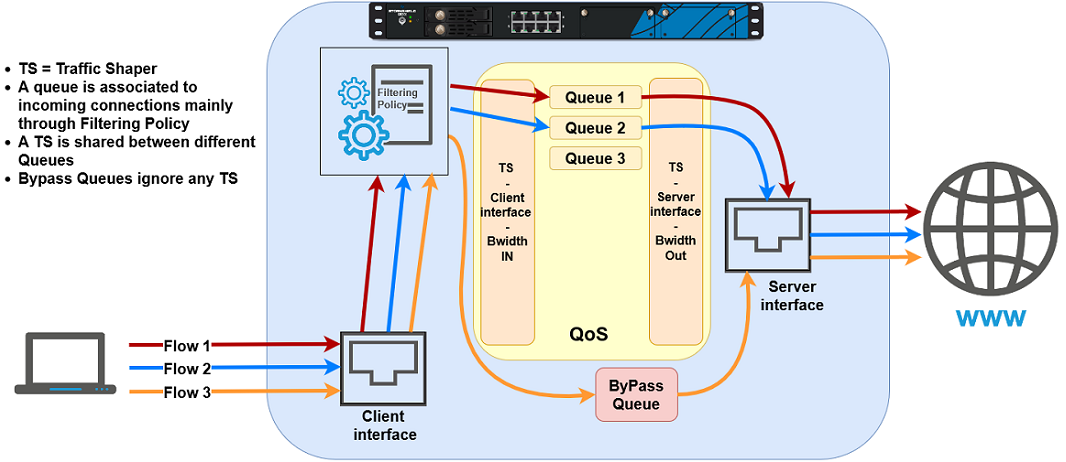
Application of QoS in LAN/WAN network traffic
Interfaces incompatible with QoS
The following interfaces cannot be selected for the application of QoS:
- GRE interfaces,
- Loopback interfaces,
- SSL VPN interfaces,
- Wi-Fi interfaces,
- LACP link aggregates,
- 4G USB modems,
- PPPoE and PPTP modems.
Using QoS through the SSL proxy
In configurations with HTTPS traffic that goes through the SSL proxy, the corresponding QoS queue must be applied to the decryption rule instead of the proxy filter rule.
Best practices
By observing some best practices, QoS can be optimally implemented:
- Configure a default acknowledgment queue (queue reserved for TCP acknowledgment [ack] packets) for each QoS-enabled network interface. Each acknowledgment queue corresponds to a 5% reservation of bandwidth on the network interface in question.
- Configure default queues for each QoS-enabled network interface. Any traffic for which no specific QoS queue has been specified will join the default queue.
- For traffic that consumes a significant portion of bandwidth, bypass queues must not be used as they have priority over all traffic and cause bandwidth reservation to malfunction. Such traffic will not be taken into account when limitation is detected on the interface and can therefore prevent QoS from activating when bandwidth is saturated on a link.
Bypass queues are to be used for traffic such as IPsec negotiation or router monitoring.
Implementation precautions
IMPORTANT
Before implementing Quality of Service (QoS) in a production architecture that was initially free of any QoS settings, Stormshield recommends that you first create a configuration based on monitoring queues (MONQ) instead of directly on class-based queues (CBQ).
This step will help you to see the volume of traffic on which no QoS is applied, and to check whether the intended bandwidth reservation or limitation values for CBQs suffice to let QoS-enabled traffic pass through.
Once these values are established, you can then set up your CBQs.
Limitations and explanations on usage
-
When QoS is enabled, non-QoS traffic will be affected by an overall decrease in throughput on the SNS firewall. This is due to the fact that traffic using bypass queues cannot use all the available bandwidth, as multi-CPU architectures are not optimally managed by the QoS engine.
Restrictions and characters allowed in queue names and traffic shaper names
QoS queues
- Names must not exceed 31 characters.
- Prohibited characters:
- Names must not contain any of the following reserved expressions:
@ [ ] # ! \ " | <space> <tab>
internet any any_v4 any_v6 firewall_ network_ broadcast anonymous none all original
Traffic shapers
- Names must not exceed 15 characters,
- Prohibited characters:
@ [ ] # ! \ " | <space> <tab>
Naming of interfaces in this Technical Note
For a better understanding of the various use cases shown, the firewall's original interfaces have been renamed as follows:
- in interface: LAN,
- out interface, WAN,
- dmz1 interface, DMZ,
- dmz2 interface, WAN2.