Creating router objects
The use of router objects makes it possible to provide redundancy between WAN links. Indeed, these routers are made up of different gateways that can be defined as active or backup.
To test the availability of these gateways, a series of ICMP requests (pings) will be sent. They are carried out over regular intervals ("frequency" setting, expressed in seconds).
Once a request has been sent to a gateway, the firewall will wait for its response for the defined period ("wait" setting, expressed in seconds). If it does not receive a response, it will send a new request until it reaches the maximum number of unsuccessful times defined ("tries" setting). Once it has reached the number of tries, and if no response has been received, the firewall will consider the gateway uncontactable. One or several backup gateways will then become the main gateway(s).
The "frequency", "wait" and "tries" settings can only be configured in the CLI:
CONFIG OBJECT ROUTER NEW name=<router name> [tries=<int>] [wait=<seconds>] [frequency=<seconds>] update=1.
The recommended values for these settings are:
- "frequency": 15 (seconds),
- "wait": 2 (seconds),
- "tries": 3.
In the configuration shown, three router objects need to be created:
- The first (HTTPRouter in the example) is used for transporting HTTP/FTP traffic on WAN1, without redundancy,
- The second (ProductionRouter) allows guaranteeing the redundancy of production traffic going from WAN2 to the two other links WAN1 and WAN3,
- The third (VoIPRouter) ensures the transfer of traffic from WAN3 to WAN2.
IMPORTANT
For the configuration of routed IPsec tunnels, the routes defined in the filter rules must use remote gateways. Router objects used in this example are therefore based on remote virtual IPsec interfaces.
Router for HTTP and FTP traffic
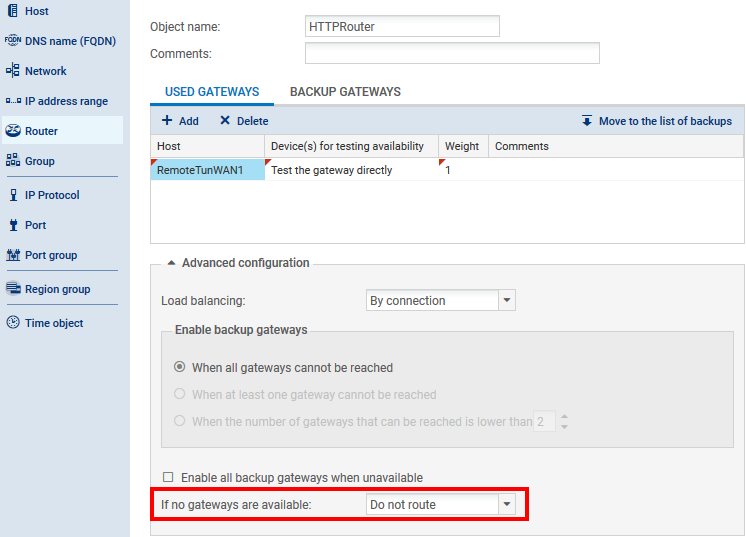
In the Configuration > Objects > Network objects menu, click on Add and on the Router icon in the upper banner.
- Enter the name of the object (HTTPRouter in the example),
- In the list of gateways used, select the remote router associated with WAN1 (RemoteTunWAN1 object in this example),
- In the object's advanced configuration, select the option Do not route for the field If no gateways are available. As such, if WAN1 fails, HTTP/FTP traffic will not be taken into account by the routing instructions defined by default. The firewall will simply ignore such traffic.
Click on Create and duplicate to confirm this configuration.
Router for production traffic
- Enter the name of the object (ProductionRouter in the example),
- In the list of gateways used, select the remote IPsec interface associated with WAN2, i.e. the RemoteTunWAN2 object in this example),
- In the list of backup gateways, add both remote IPsec interfaces that are likely to receive production traffic if WAN2 is unavailable, i.e. RemoteTunWAN1 and RemoteTunWAN3,
- In the object's advanced configuration, select the option Enable all backup gateways when unavailable: both backup gateways RemoteTunWAN1 and RemoteTunWAN3 will then be simultaneously enabled when the main link WAN2 becomes unavailable:
NOTE
If different weights are assigned to both backup gateways, load balancing for new connections will be applied when the main gateway fails.
EXAMPLE
A weight value of 50 is assigned to the gateway RemoteTunWAN1.
A weight value of 10 is assigned to the gateway RemoteTunWAN3.
When both of these gateways become active, the gateway RemoteTunWAN1 will absorb 50/(50+10)=83% of connections. The remaining 17% of connections will be managed by the gatewayRemoteTunWAN3.
Router for VoIP traffic
In the Configuration > Objects > Network objects menu, click on Add and on the Router icon in the upper banner:
- Enter the name of the object (VoIPRouter in the example),
- In the list of gateways used, select the remote router absorbing WAN3 (RemoteTunWAN3 object in this example),
- In the list of backup gateways, add the gateway that is likely to receive VoIP traffic if WAN3 is unavailable, (RemoteTunWAN2 in the example):