Configuring the VPN client
On the user's Microsoft Windows workstation:, open the connection window of the VPN client:
- Right-click on the icon found in the Windows system tray (hidden icons):

- Select Connection panel.
Configuring Phase 1
- In the VPN configuration tree, right-click on IKEv1.
- Select New Phase 1.
An entry named Ikev1Gateway by default is added to the IKEv1 tree. - Right-click on Ikev1Gateway and select Rename to give this entry the name of your choice (IKEv1GwConfig in the example).
- Click on this entry.
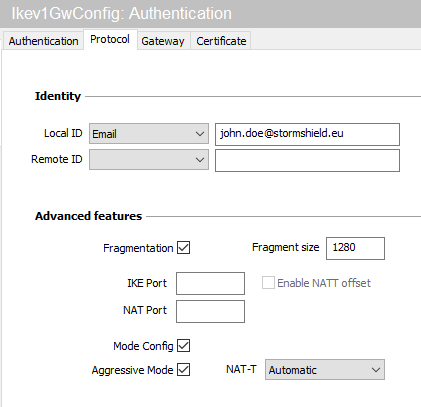
- In the Protocol tab > Identity > Local ID field, select E-mail from the drop-down list and enter the e-mail address of the workstation user.
- In the Protocol tab > Advanced features section, select the Fragmentation checkbox and indicate the size of IKE fragments as defined on the firewall (1280 bytes according to Stormshield’s recommendations).
- Select the Config mode and Aggressive mode checkboxes as well.
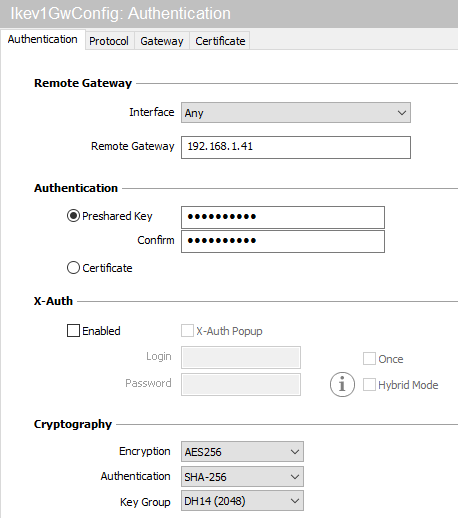
- In the Authentication tab > Remote router address > Remote router address field, enter the public IP address or FQDN of the firewall with which the VPN client must set up a tunnel.
If you choose to use an FQDN, ensure that the DNS servers on the workstation have resolved it before you set up the tunnel. - In the Authentication tab > Authentication > Preshared key field, enter and confirm the pre-shared key defined for this user on the firewall.
- Click on the upper menu Configuration > Save to save this configuration.
Configuring Phase 2
- In the VPN configuration > IKEv1 tree, right-click on the Phase 1 configuration created earlier (IKEv1GwConfig in the example)
- Select New Phase 2.
An entry named Ikev1Tunnel by default is added to the selected Phase 1 configuration. - Right-click on Ikev1Tunnel and select Rename to give this entry the name of your choice.
- In the IPsec tab > Addresses > Address type field, select Network address.
- In the Remote network address field, enter the address of the first reachable network (192.168.1.0 in the example).
- In the Subnet mask field, enter the mask associated with this network (255.255.255.0 in the example).

The VPN client is now configured to set up an IKEv1 tunnel in Config mode with the firewall.