Using default behavior and specific behavior in rules
In access control rules, you can apply a default behavior or action and one or several specific actions.
Define specific actions if you want to allow or block access from identified applications to the resource targeted by the rule.
You can add several specific actions in the same rule: one for example, to allow certain applications, and one to block others. In this case, the order of specific actions matters: if an application in the first specific action can access the resource, the rule applies and the second specific action will not be read.
In a protection rule set, enable default behavior when you want to ensure that access to the resource will be blocked or allowed, regardless of which rules follow.
EXAMPLE 1
In code execution rules:
- To prevent the DLL *\lxssmanager.dll from running on all applications, enable default behavior with Execution = Block.
- To prevent the DLL *\system.management.automation.dll from running on all applications except legitimate applications, enable default behavior with Execution = Block and add a specific action Legitimate applications = Allow. 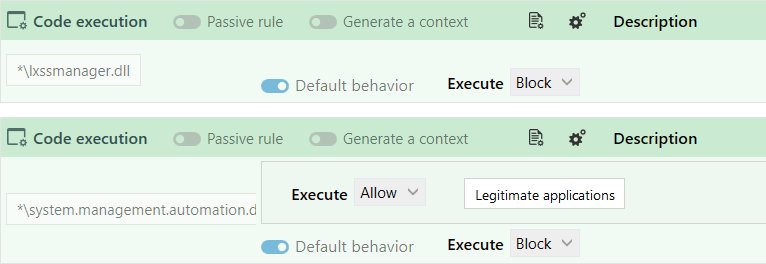
EXAMPLE 2
In file access rules:
To always allow the account NT SERVICE\TrustedInstaller to run powershell scripts (*.ps), enable default behavior with Read = Allow.
In the examples above, access will ALWAYS be allowed or blocked. Enabling default behavior means that rules for the resource in question will no longer be read. As such, any rules placed after this rule will not apply.
In audit rules, the default behavior is ignored, and all rules will be read every time.
In a protection rule set, disable default behavior when you want to ensure that the next rule affecting the same resource will be read.
- In the file access rules, to ensure that different log levels are generated according to which applications access the same resource, disable default behavior on the first rule, add a specific action to block certain applications, and apply a specific log level.
Next, create a second rule with a different specific action and a different log level. - In the process access rules, create the first rule to grant the Windows task manager all permissions to all processes and disable default behavior. With this configuration, the task manager will never be blocked by subsequent rules that may prohibit some applications from accessing some processes that may include the manager.