Cross-encrypting secure messages
Cross-encryption makes it possible to update the protection level of secured messages. It consists of re-encrypting with your new key any message encrypted with a former encryption key and by using the default encryption algorithm defined in the user account.
The former encryption key may be out of date for the following reasons:
- The encryption key has been renewed,
- The user account has been updated and the encryption key became unusable, For example, when switching from a password account to a smart card account, or when a key is revoked or comes from another encryption system, etc.,
- The encryption key was sent by a third party, for example when privileges are transferred during the user's transition to a new position.
To cross-encrypt a secured message, the former encryption key is needed in order to decrypt the message first. The key must be in the keycase as a decryption key.
Once the message is cross-encrypted, only the new key is able to decrypt it.
Messages and attachments are cross-encrypted to their original formats: if they are in .sbox, they will remain in .sbox after cross-encryption.
NOTE
A delegation key cannot be used for cross-encryption because it only allows secured messages to be read.
The way the cross-encryption process behaves with coworkers is as follows in both cases:
- When a secure S/MIME file sent to several recipients is cross-encrypted, it will be secured only for the current user. Coworkers will not be affected as only the local personal copy of the message is cross-encrypted.
- When a plaintext message with a secure attachment is cross-encrypted, only the security level of the attachment is updated. If this attachment is forwarded to coworkers declared in the original .sbox file, and if their certificates are still valid, they will still be able to access the attachment.
As for recovery accounts associated with user accounts, they will still be embedded in cross-encrypted messages.
Cross-encryption is an operation that is performed on a folder in your Outlook client and all its sub-folders.
- Select the folder to cross-encrypt.
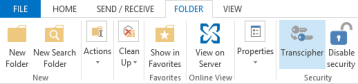
- Right-click on the folder and select Cross-encrypt or click on Cross-encrypt the Folder tab from the main ribbon.
- In the cross-encryption window, click on Cross-encrypt. Information about the operation is displayed during the process.

- At the end of the process, a report shows the number of cross-encrypted messages and the number of errors. If errors occurred, click View report.
The report gives details about the errors for each e-mail impacted:
- The user does not have a valid encryption key,
- The user only has a delegation key,
- An error occurred during the processing of the message,
- The File feature is not installed (in case the message contains a secure attachment).
The report file is named SBoxTransciphermentReport-<utilisateur>-<horodatage>.txt and is stored in the user's temporary folder. The file remains in this folder.
NOTE
To access the user's private keys during cross-encryption, you must be connected to the SDS Enterprise account.
The progress window prevents any interaction with Outlook during the process. Despite this, if cross-encryption is disrupted, the user must manually restart the process.
Cross-encryption cannot support some cross-encrypted message configurations:
- Secure attachments contained in secure S/MIME messages are not cross-encrypted,
- Secure messages sent as .msg attachments in a plaintext message are not cross-encrypted.
Messages encrypted with OpenPGP cannot be cross-encrypted.